Nino Vales
Nino regularly writes tips and articles about Cybersecurity. He holds multiple Cybersecurity certifications (CISSP, CySA+, CyberOps, M365:Security Administrator). During his free time, he loves to go fishing and camping. He is a basketball fanatic and collects limited edition basketball sneakers and jerseys.

Exchange Online Data Loss Prevention in Microsoft 365 Business Premium
Latest Posts
What is an MFA Bombing Attack and How to Avoid Being Compromised
Know more about the MFA bombing tactic Many of us already know the importance of having Multi-Factor Authentication or MFA. Enabling MFA gives many users peace of mind against..
Is It Time to Review Your Cybersecurity Policies?
With recent global developments, we've seen an increased risk to organizations that are not prepared for potential cyber attacks. Learn what to look out for and how to get ahead..
Webinar with Cisco: 10 Myths for SMB Cybersecurity…Busted!
Missed Cisco and Clear Concepts' live webinar on “10 Myths for SMB Cybersecurity…Busted!”? Check out the recorded webinar here!
Things to Remember about Email Passwords
An email account with a simple or weak password puts your information at risk. Confidential attachments, messages, bank information, contact list, or personal conversations could..
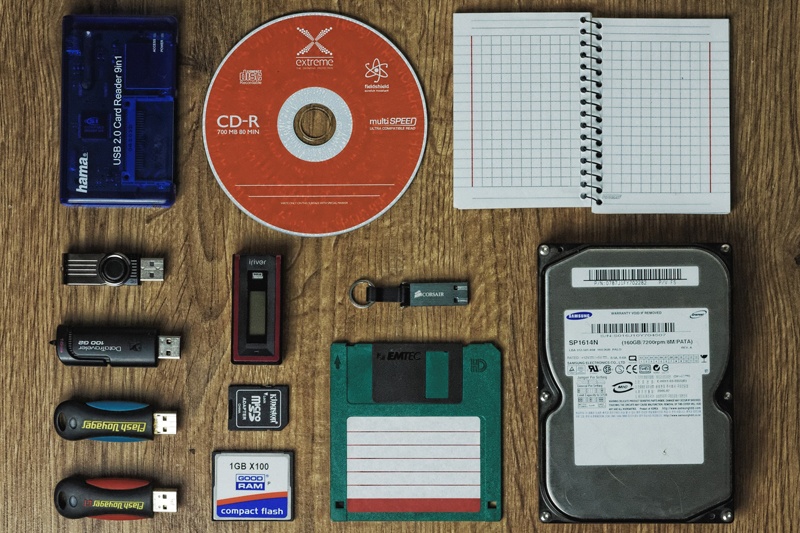
Explaining the 3 2 1 Backup Rule
The more backup copies you have, the better your coverage against losing a full day of work or even worse your entire data. Ransomware, data corruption, accidental deletions, or..
Cyber Kill Chain & Ransomware
The Cyber Kill Chain model breaks down a Ransomware attack in seven stages. This article will give you an understanding of our security solutions and what is effective based on..
Protect Yourself Against Macros and Malicious Websites
Macros – they are normally delivered as attachments in the form of a Microsoft Word document. Macros can either make your life easier by automating those repetitive stuff or..
Protect your Backups from Ransomware
Ransomware scans network locations where the infected user has read and write access. Files under documents, desktop, and the shared folders you have access are examples of..
Risks of Unsecured Remote Desktop Connections
The ability to connect to your work computer or remote desktop server remotely provides added productivity to some employees. However, the risks of having this incorrectly..