Adopting MFA Series Part 2: MFA Apps

At Clear Concepts, we are passionate IT professionals who want to make a positive impact on your business operation. We understand the value of Information Technology and how it can deliver a return on investment for your organization. We serve a wide variety of business networks, with a focus on businesses between 10 and 500 employees. If you are looking to take your business to the next level, we are the team you need!
The following vertical markets are examples of how we can make an impact but we also serve other business types not featured on our website. From Manufacturing to Retail, Banking to Real Estate, we have the knowledge and expertise to help you succeed. Contact us today to find out how we can help you reach your goals!



Affiliation:

In part 2 of our "Adopting MFA" series, we'll take a quick look at a few of the most popular authentication apps available today.
.jpg?width=700&name=Hubspot%20Featured%20Images%20v3%20(2).jpg) Original photo by Franck on Unsplash
Original photo by Franck on Unsplash
Regardless of whether you're protecting a personal or business account, you have a few mainstream applications that help make things a bit easier. I mentioned them briefly in part 1 of this series, but we'll take a closer look at them in this post.
Starting with a Microsoft product? Hold your shocked expressions for a moment, please.
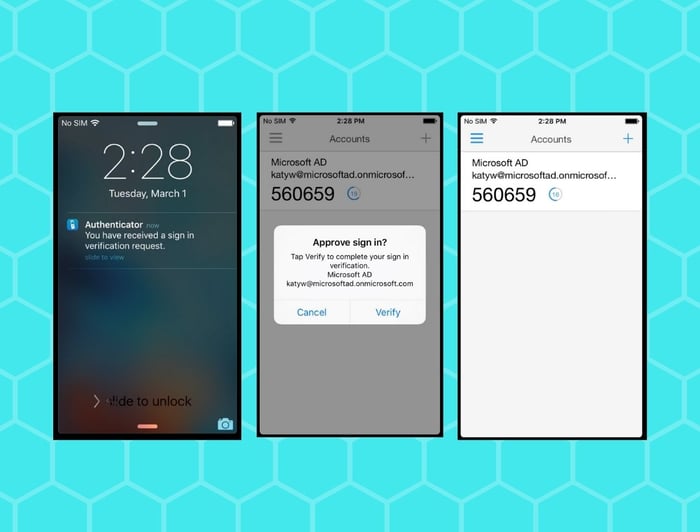
Microsoft's Authenticator app is a great place to start if you are an Office 365 user, and/or have personal Microsoft accounts that you want to secure. Of course, Microsoft Authenticator isn't limited to only Microsoft accounts, so there's every reason to check out this app.
Click here to get the Microsoft Authenticator app.
Google Authenticator is another terrific option in makes securing your accounts as easy as possible. This app is part of Google's 2-Step Verification account verification options and specifically handles the generation of one-time passcodes.
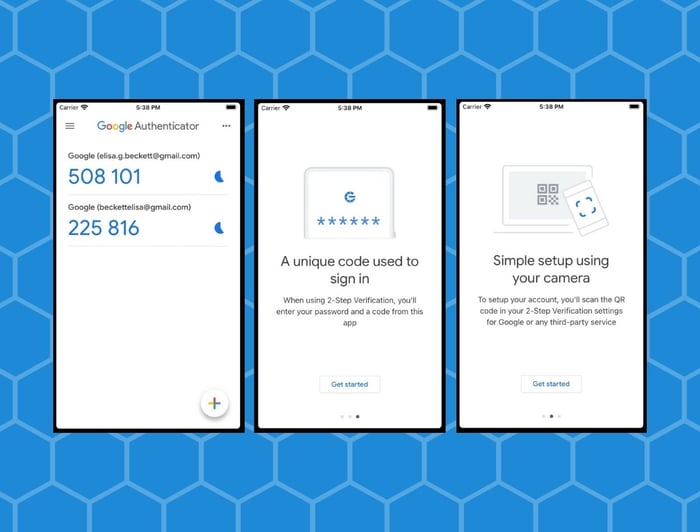
Unlike Microsoft's solution, the Google Authenticator app does not offer features like password-less login with biometrics or a PIN. However, Google's 2-Step Verification features does include text messages, phone calls, and even physical USB security keys.
Lastly it's (also) free for Android and iOS devices! Click here to get setup Google Authenticator.
Unlike Google and Microsoft's solutions, Duo MFA is mainly (but not exclusively) geared towards enterprise users instead of the general public. So if you're an IT admin or small business owner, then this may be the right solution for you.
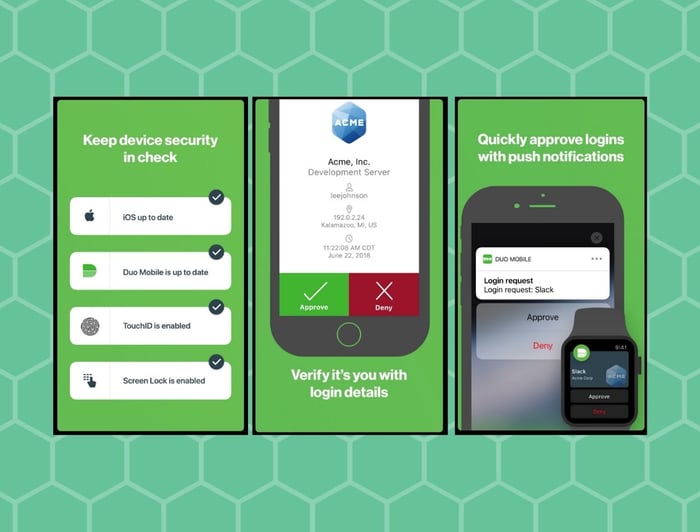
Additionally, Duo MFA is a paid service priced at $3/user/month (at the time of writing this). While there is also a free version of the MFA app, if you're planning to roll this out to your organization then I recommend looking at their free trial instead.
The big advantage with choosing Duo for your authentication needs is their specialization in the enterprise market. In addition to supporting cloud-only, on-premise and hybrid environments, they have the administrative tools to help you rollout and manage devices.
Click here to learn more about Duo MFA and pricing.
In the next (and final) article on this series, we'll get into how to go about implementing MFA in your organization. If you're already convinced and are ready to step-up your organization's cyber-security, give us a call!
Ready to learn more? Read the next article.